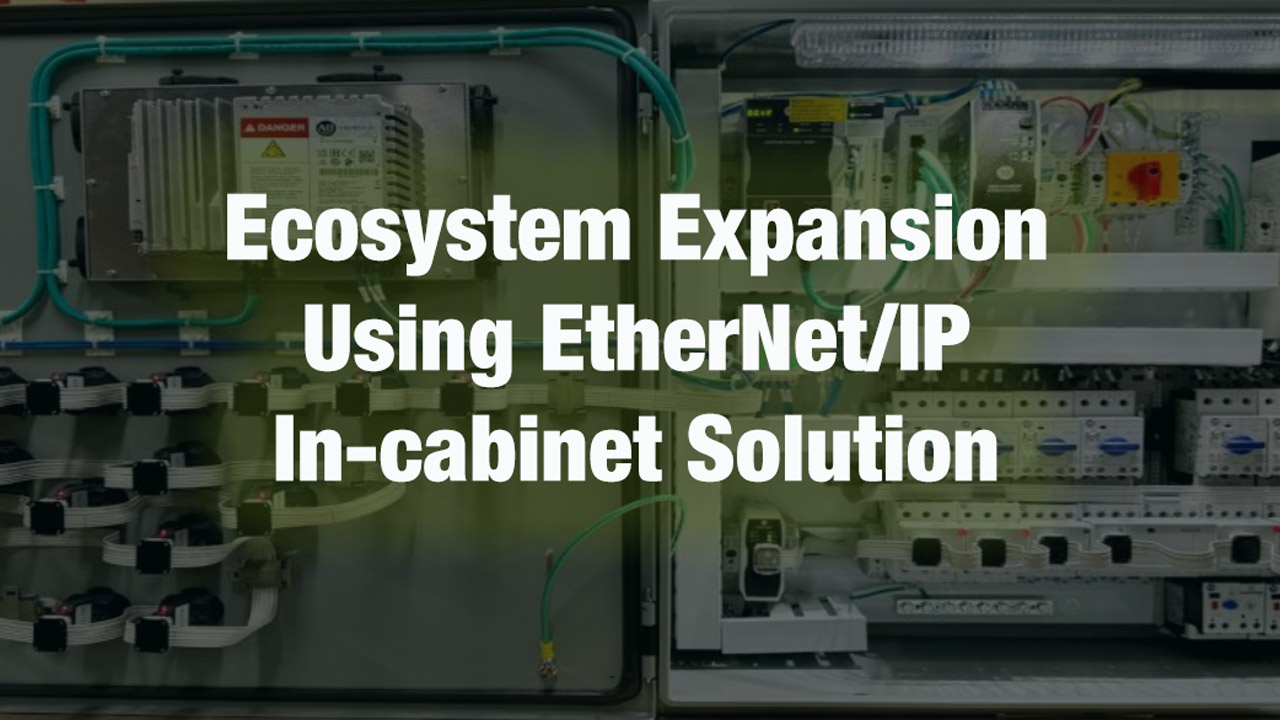
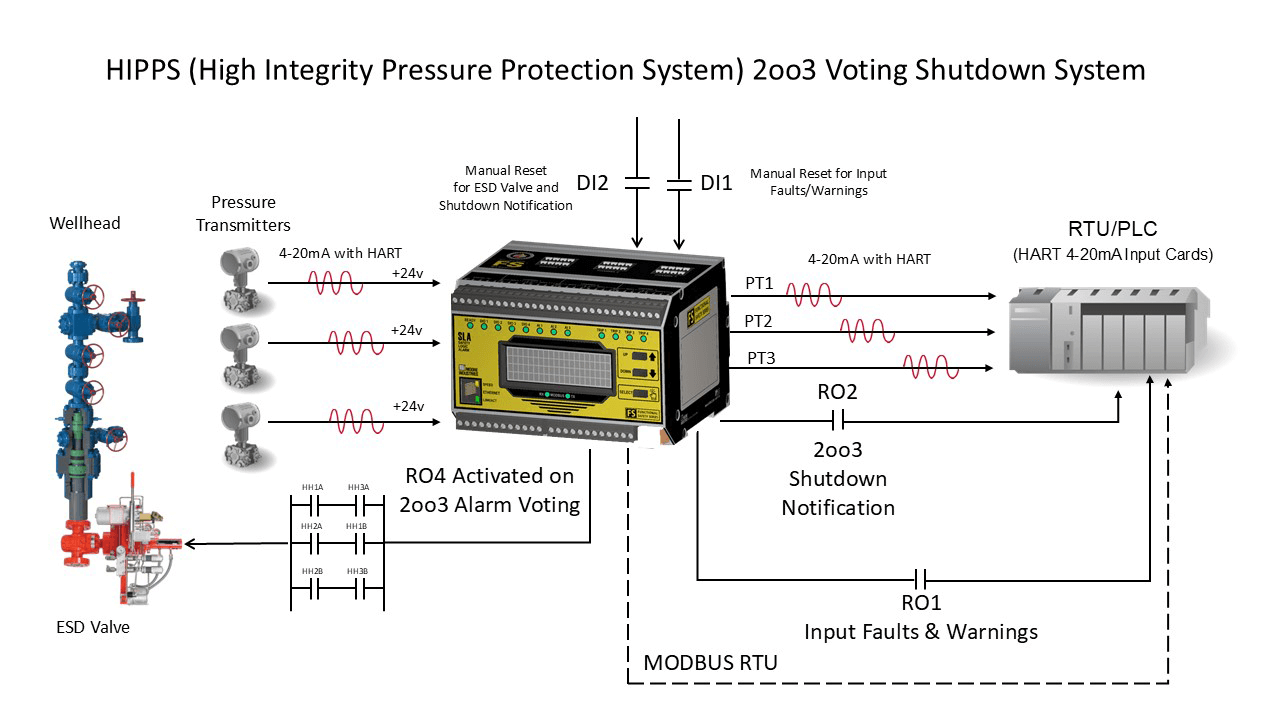
TECHNOLOGY HIGHLIGHT
Challenges of a High-Density and Non-Concentrated Temperature Monitoring System
The traditional approach to temperature monitoring in process control applications involves challenges that can increase initial setup and ongoing maintenance costs, while also complicating monitoring system management and reducing operational efficiency.