TechnologyJanuary 18, 2023
Technical approaches to defend and protect IoT nodes
Creating a secure IoT node begins with a “root of trust”, a small affordable integrated circuit designed to offer security-related services to the node. Examples are data encryption for preserving confidentiality and digital signatures to ensure authenticity and integrity of information.
Ten billion IoT nodes are connected today, ten times more than just a decade ago, and the trend is continuing unabated. With this growth comes an equal growth of opportunities for attackers of industrial and manufacturing facilities.
The estimated annual cost of cyber attacks ranges from tens of billions of dollars to over a trillion, and it too keeps rising. Therefore, security considerations are now essential to continue the successful scaling of the IoT. IoT security begins with the security of the IoT nodes.
No company wants to see its name in the same sentence as “breached, and customer data was stolen.” What’s more, connected devices are also subject to government regulations, such as FDA rules for medical devices, US/EU cybersecurity requirements for Industry 4.0 critical infrastructures, and several new emerging standards for the automotive industry.
Those requirements push for high-level security while not explicitly mandating the use of hardware-based security. However, IoT nodes are often large-volume, cost-optimized appliances, creating challenges to balance security and cost.
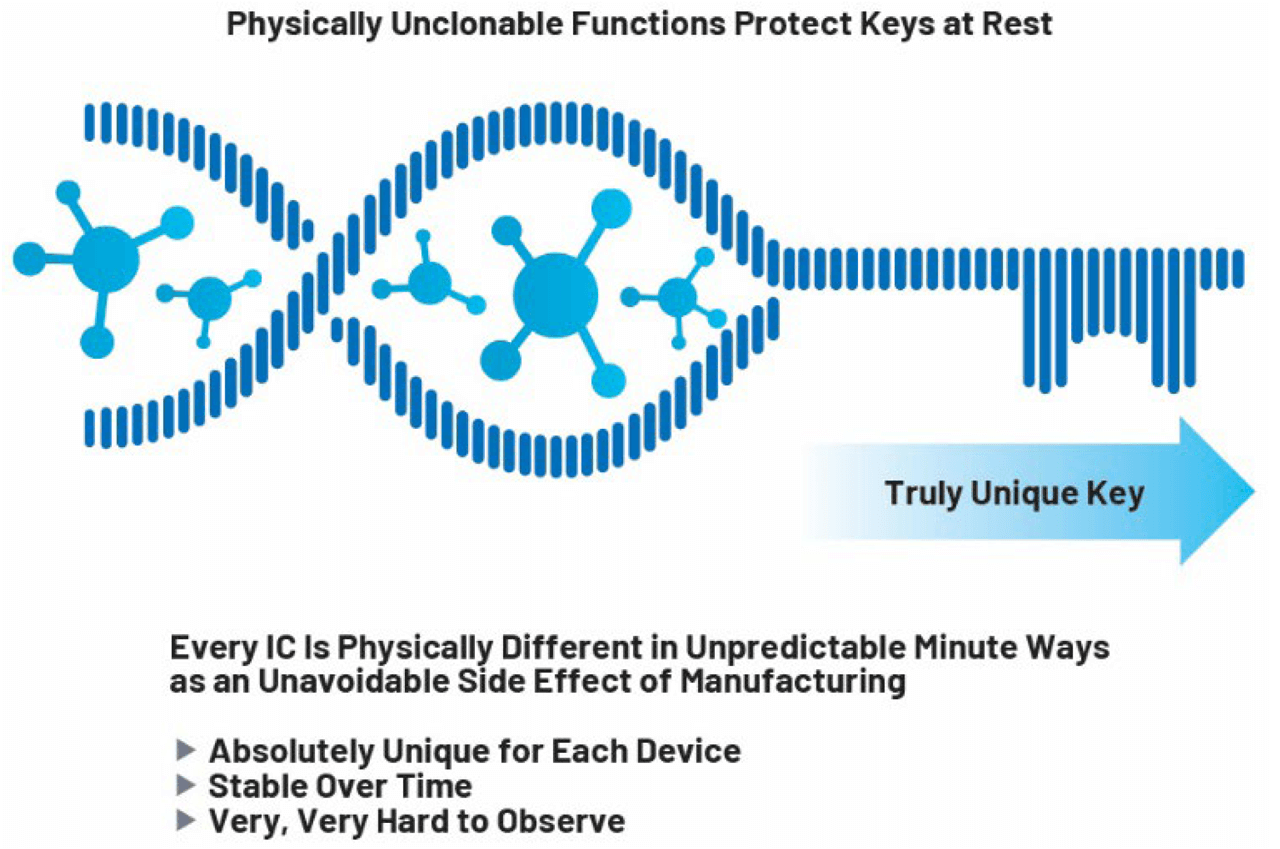
Figure 2. PUF technology mitigates the risk from direct probing of microcircuits.
Secure nodes Using “Roof of Trust”
How can we design a cost-efficient yet secure IoT node? Creating a secure IoT node begins with a “root of trust” (also known as “Secure Element”), a small affordable integrated circuit designed to offer security-related services to the node.
Examples of these functions are data encryption for preserving confidentiality and digital signatures to ensure authenticity and the integrity of information. The ultimate goal of the root of trust is to ensure that the secret keys used for data encryption or digital signatures are protected against disclosure.
The biggest challenge for “root of trust” security ICs is resistance against physical attacks, such as direct probing and so-called side-channel attacks.
Physically unclonable function (PUF)
Unfortunately, because direct probing attempts to observe internals of microcircuits, memory technologies typically used in general-purpose microcontrollers (i.e., EEPROM or Flash) are not secure.
An attacker can directly observe the memory contents at a relatively modest cost using Scanning Electron Microscopy (SEM). The semiconductor industry has developed the “physically unclonable function” (PUF) technology to mitigate this risk. The PUF is used to derive a unique key from the intrinsic physical properties of the chip. Those properties are far more difficult to probe directly, making it impractical to extract the resulting key via direct probing. In some instances, the PUF-derived key encrypts the rest of the internal memory of the root of trust and, therefore, protects all other keys and credentials stored on the device.
Side-channel attacks are even cheaper and less intrusive. They leverage the fact that electronic circuits tend to leak a signature of the data they are manipulating, for example, over the power supply, radio, or thermal emissions.
The subtle correlation between measured signals and the processed data can lead to successfully guessing the value of a secret key after a moderately complex statistical analysis when the circuit uses that key, for example, to decrypt data. A root of trust is explicitly designed to prevent such data leakage using various countermeasures.
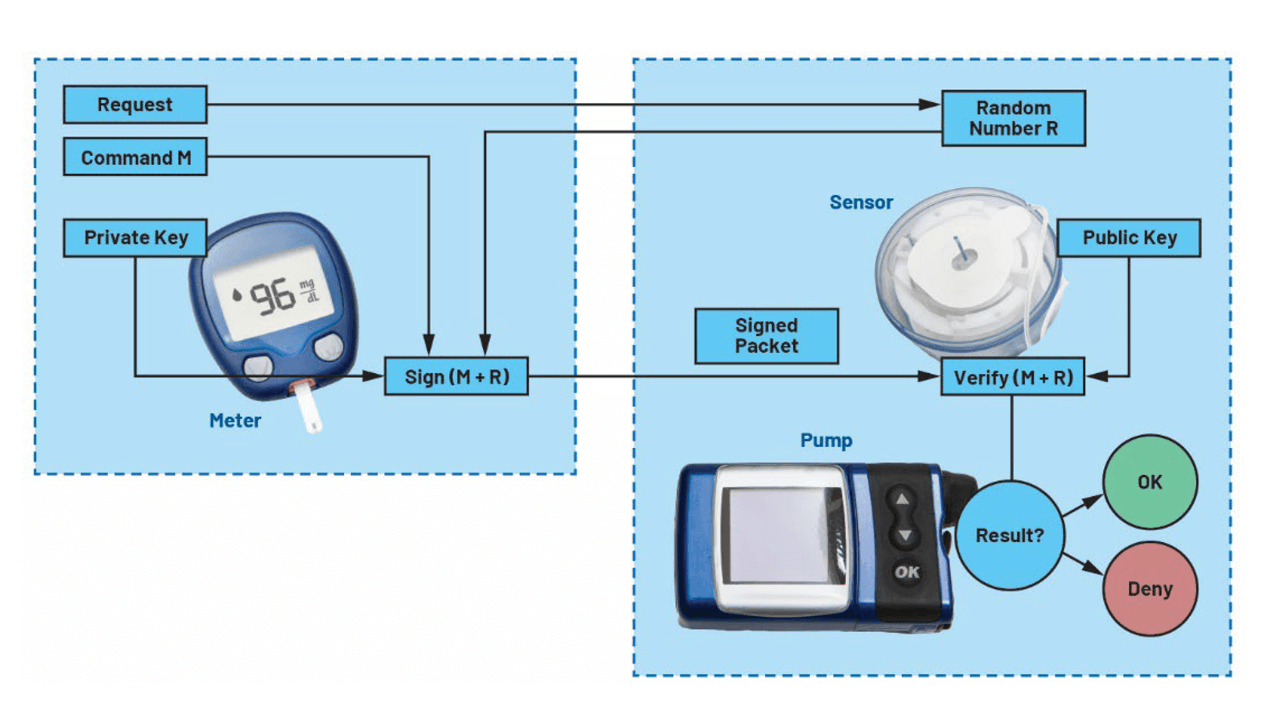
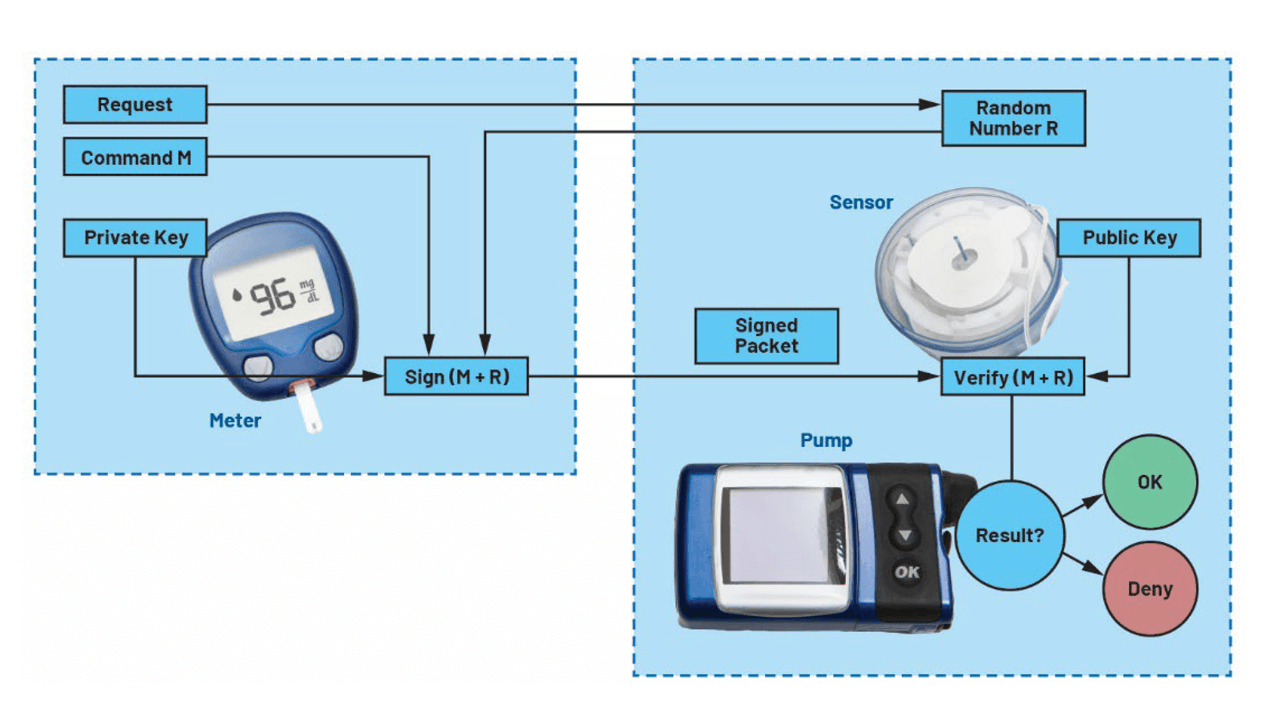
Figure 3. Insulin pump authentication is a simplified example of root of trust.
Application Example Using a Security IC
The benefits of a hardware-based “root of trust” become evident in the type of secure applications depicted in Figure 3. The protocol used is a simple challenge/response authentication protocol:
- The meter requests a challenge from the pump in preparation for sending a command.
- The pump challenges the requestor with a random number R.
- The meter uses its private key to sign the command, the random number R, and some fixed padding. This operation is deferred to the “root of trust” of the meter.
- The pump verifies that the signature is correct and that the random number is the same number it sent out earlier to avoid the trivial re-sending of a valid command. This operation is deferred to the “root of trust” IC of the pump.
In addition to the fact that every new attempt at sending a command requires a new random number, the security of this protocol relies on the secrecy of the private key used to authorize commands and the integrity of the public key used to verify the authorizations. If these keys were stored inside common microcontrollers, they could be extracted or manipulated, and fake meters or pumps could be manufactured, potentially endangering the patients’ safety.
In this case, “root of trust” ICs make it much more difficult to counterfeit meters or pumps, manipulate the credentials, or tamper with the communication protocol.
Benefits of dedicated security ICs
Overall, a sound node device design will cause the cost of breaking a device to be much higher than the potential rewards for the attacker. The benefits of an architecture relying on a dedicated security IC are numerous:
IoT security is an endless battle. Attack techniques keep improving but, at the same time, security IC vendors continue to enhance their countermeasures so that security ICs remain extremely costly to attack. The security of a connected device can be increased by upgrading the security IC with little impact on the overall device design and cost.
Concentrating the critical functions in a strong, tamper-proof physical environment separated from the application processor allows for an easier “proof of security” when evaluating regulatory compliance. Isolation also makes it harder to leverage weaknesses in the device’s application processor, which are very difficult to detect and remove entirely.
Ensuring the security of an IoT node across all its life cycle is easier when the security IC is commissioned early by the security IC vendor. This approach eliminates the need for sharing critical information with contract manufacturers, and a secure personalization flow and secure OTA updates are made possible. Overbuilding and cloning become much harder as well.
Conclusion
There are many components in a typical connected system, and security must be designed in from the beginning. While securing IoT nodes is not the only step, it is a necessary step.